The SANS Institute is one of the most trusted resources for IT professionals and they provide many resources for free. Some of these resources include posters in their “Secure the Human” section that can be displayed in employee areas that emphasize social engineering protection and training for current cyber threats.
Free tools, that are very underutilized.
I was talking with Tom Jelneck recently in our “Tech Talk Podcast” about how you can tell a good IT person. One trait is that they have no hesitation in giving out the “secret sauce” to staying protected. (See link to our Podcast below)
We love sharing the best ways to stay protected because it causes us pain to see people who suffer data loss just because they didn’t have the knowledge to be prepared.
Simply starting the conversation about security with your employees will increase your security posture, and the SANS posters are a great place to start that conversation. Verizon’s 2018 Protected Health Information Data Breach Report found that 58% of protected health information security incidents involved internal personnel, making healthcare the only industry where employees represent the biggest threat to their organizations.
In their 2018 Cyber Security Intelligence Index, IBM reports that inadvertent insiders were responsible for more than two thirds of total records compromised in 2017. More than one-third of this stemmed from attackers attempting to trick users into clicking on a link or opening an attachment.
These statistics emphasizes the need for organizations to create a dynamic cybersecurity awareness program that adapts to current threats.
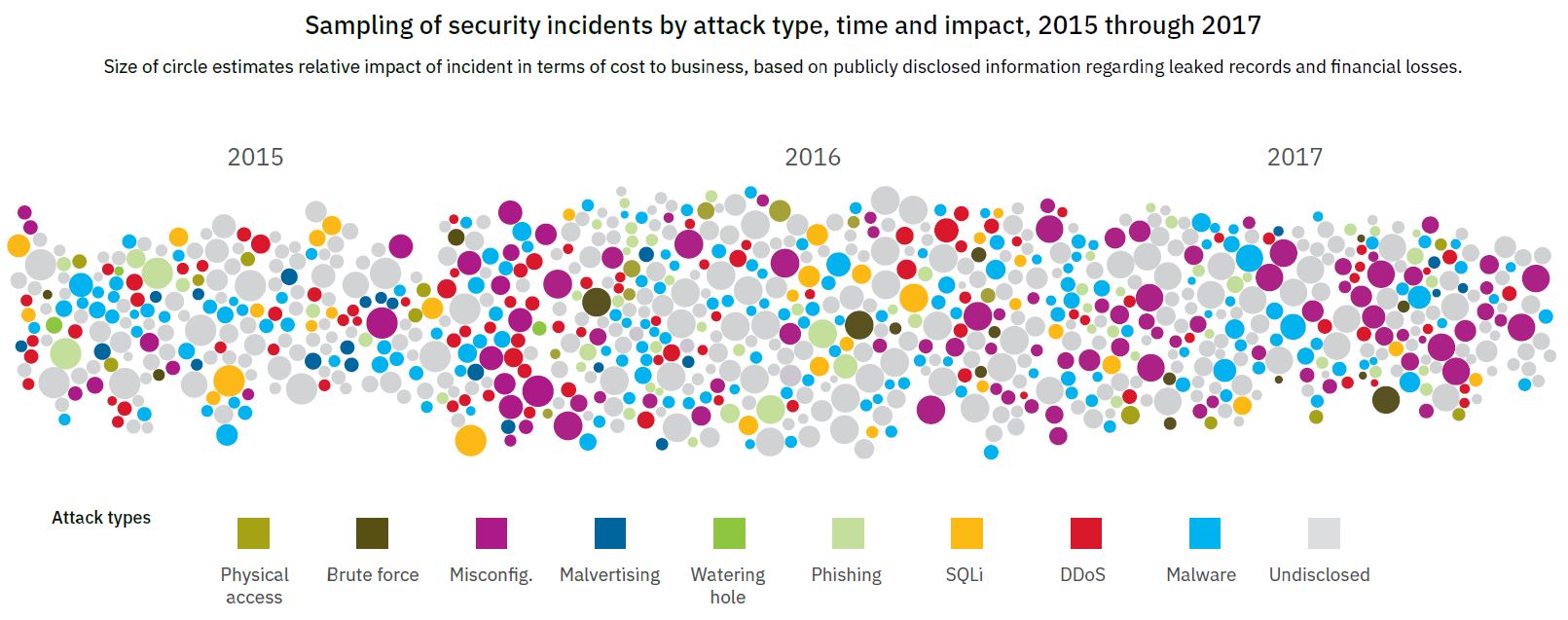
Start on the back-end, ensuring that system access is restricted as appropriate, and create policies to review access levels on a regular basis. Ensure that the physical access of sensitive areas and security of hardware, including mobile devices, is addressed. Note that the IBM report listed “Misconfig” as being responsible for the largest amount of security incidents in 2017.

Then, establish written acceptable use policies clearly outlining who can access sensitive data and when, and the consequences of accessing data without a legitimate reason. Reinforce those policies with routine monitoring for unusual or unauthorized behavior.
Lastly, make your security strategy a prominent part of system onboarding discussions and incorporate the security plan into your organizations strategic plan. Email security tips to employees on a routine basis. This will help to keep the topic of security more dominant in the workplace and assist in keeping your organization safe and secure!
We at Advanced Systems Solutions have helped to ensure that many organizations are safe and secure. If you’re looking for a support company to ensure your data stays safe, with unmatched customer service, please contact us. We love to help!
Like our Facebook page by clicking on the icon at the top right of this page to stay up to date with date with current alerts and information!
Disclaimer: The above information is not intended as technical advice. Additional facts or future developments may affect subjects contained herein. Seek the advice of an IT Professional before acting or relying on any information in this communiqué